Security firm Jamf Threat Labs released a report in January stating that the Predator spyware has a “stealth” function, which can forcibly turn off the green or orange privacy indicator light on the screen after illegally accessing the iPhone’s camera or microphone.
Starting with iOS 14, Apple introduced a privacy indicator light at the top of the screen (green dot represents the camera, orange dot represents the microphone), which is considered a core defense for users to determine whether they are being secretly photographed or recorded.

Security researchers at Jamf Threat Labs recently discovered that the commercial spyware Predator has breached this defense. After an iPhone suffers a kernel-level intrusion, this malware can use specific techniques to turn off indicator lights during malicious recording, thus deceiving users into believing that the device is secure.
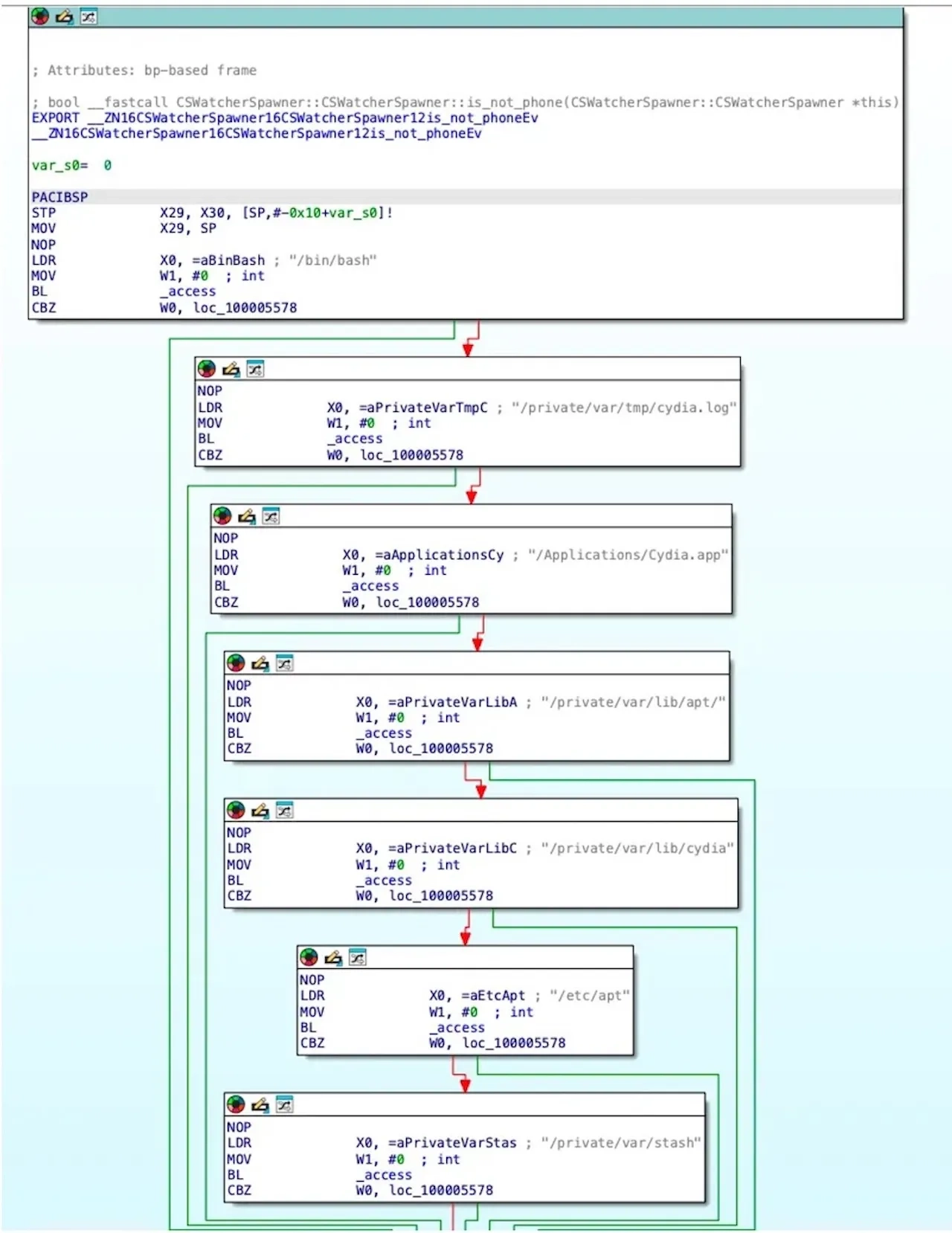
In terms of technical implementation, Predator achieves “stealth” by injecting malicious code into SpringBoard, the system interface manager of iOS.
Under normal circumstances, when a sensor is activated, the system sends a signal to SpringBoard to turn on the indicator light. Predator intercepts this signal using a “hooking” technique and sends it to a nil object.
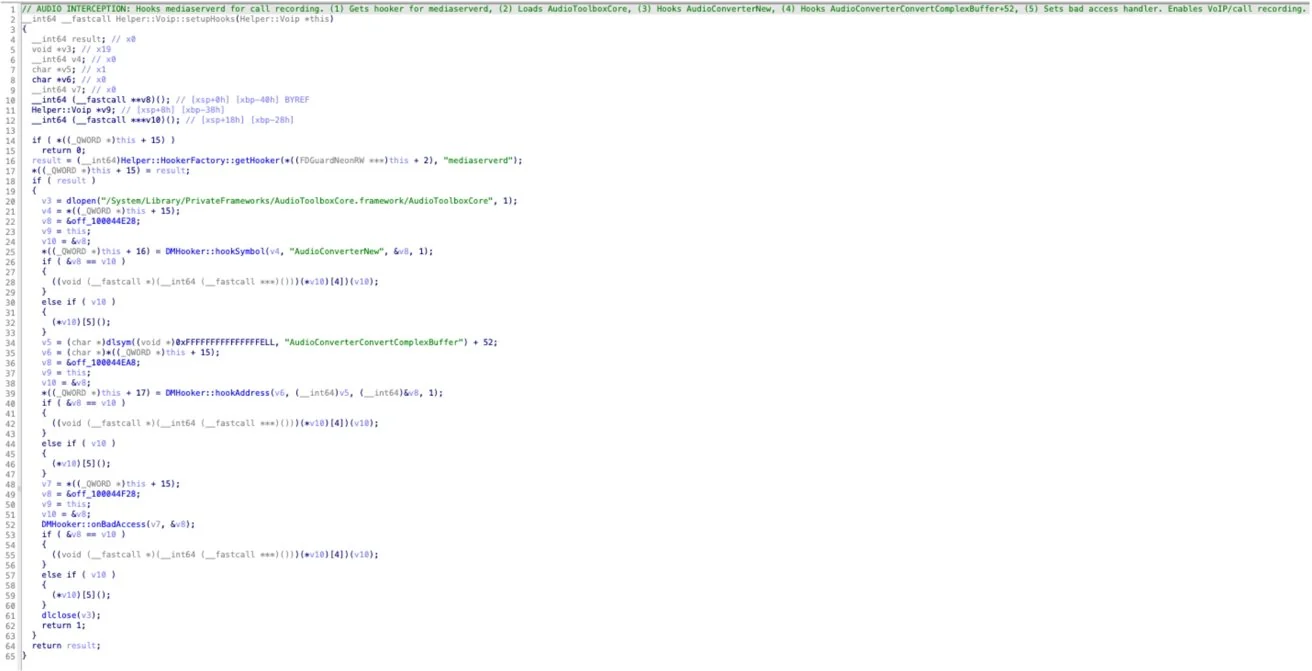
In Objective-C, messages sent to an empty object are silently ignored. Therefore, the system mistakenly assumes no recording has occurred, and the indicator light naturally doesn’t illuminate.
The most dangerous aspect of this attack is its extremely high degree of stealth. Unlike earlier malware that could cause phones to overheat, lag, or malfunction, iPhones infected with Predator show almost no abnormalities in appearance or function.
The app launches normally, notifications are pushed as usual, and even battery life may not show any noticeable change. Without the user’s knowledge, their conversations and the surrounding environment may be secretly recorded and uploaded.
According to a blog post cited by Free Tech News, this type of attack is a “post-compromise,” meaning that hackers must first gain root access (kernel access) to the device through zero-day vulnerabilities or other means before they can carry out their attack. Such attacks typically target specific high-value individuals such as journalists and politicians; the probability of ordinary users encountering this risk when downloading apps from the App Store is extremely low.



