Jamf, an Apple device management and security company, released a report yesterday (April 8) stating that the ClickFix attack method on the Mac platform has been upgraded. Attackers have abandoned the traditional terminal copy-paste mode and instead use the system’s built-in script editor as a breakthrough point.
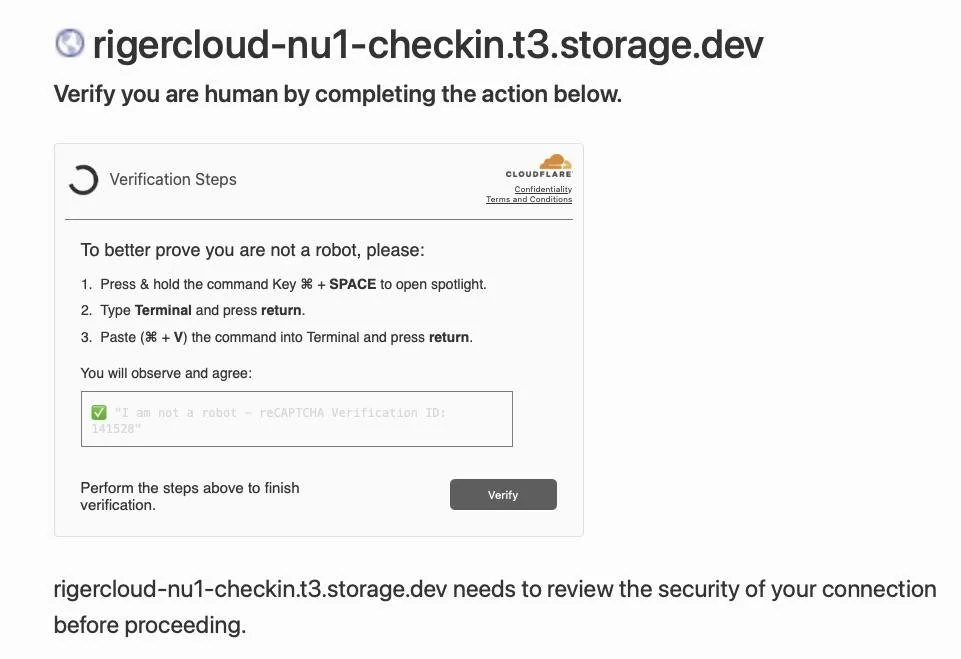
It was reported in March of this year that hackers launched a new attack method called ClickFix, which tricks Mac users into installing malware through a fake human verification page.
Security researchers point out that the number of ClickFix attacks detected surged by more than 500% between 2024 and 2025, making it one of the fastest-growing social engineering threats on the internet.
How The ClickFix Attack Works
Victims who visit compromised websites or click on malicious ads are shown a fake CAPTCHA page. Unlike regular image recognition or checkboxes, this page instructs users to open the system’s built-in “Terminal” tool and paste a seemingly complex command to complete the “verification.” Therefore, Apple introduced a paste command scanning mechanism in the macOS 26.4 update to mitigate this risk.
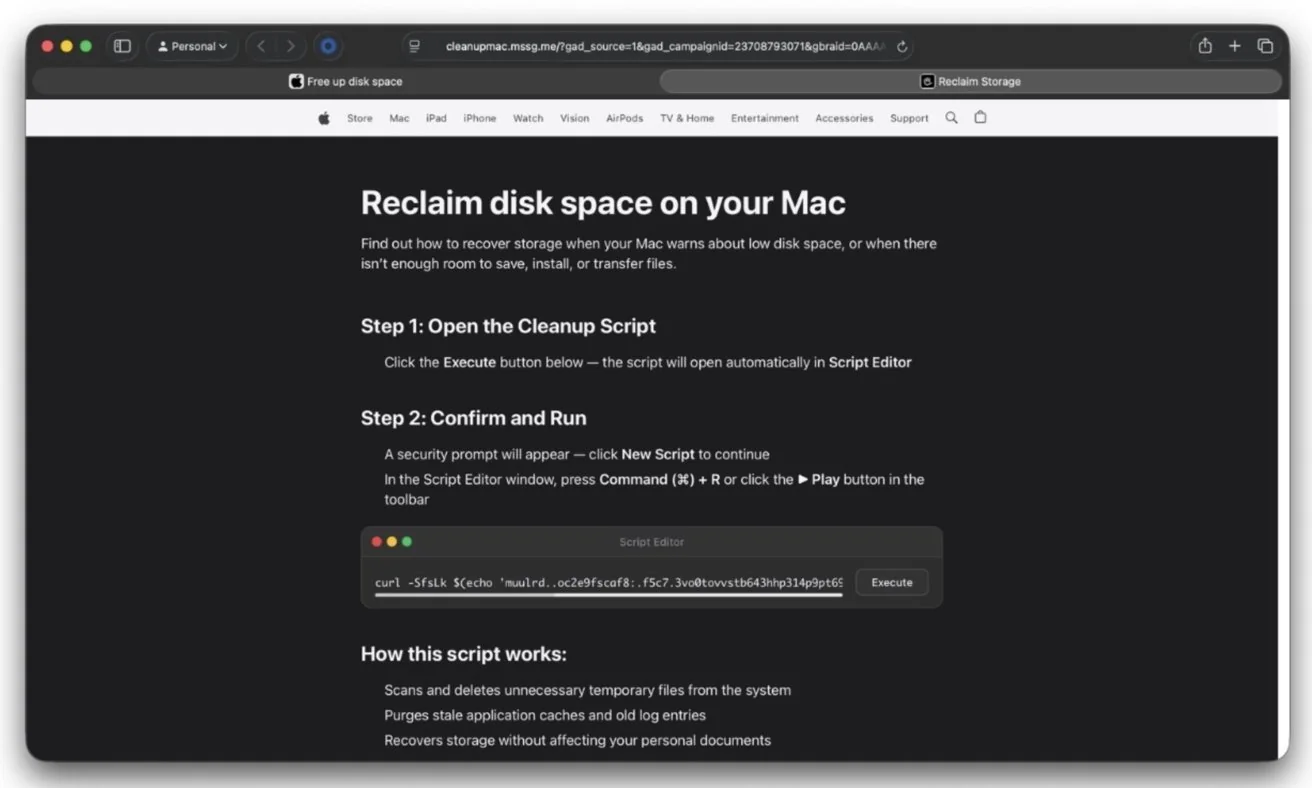
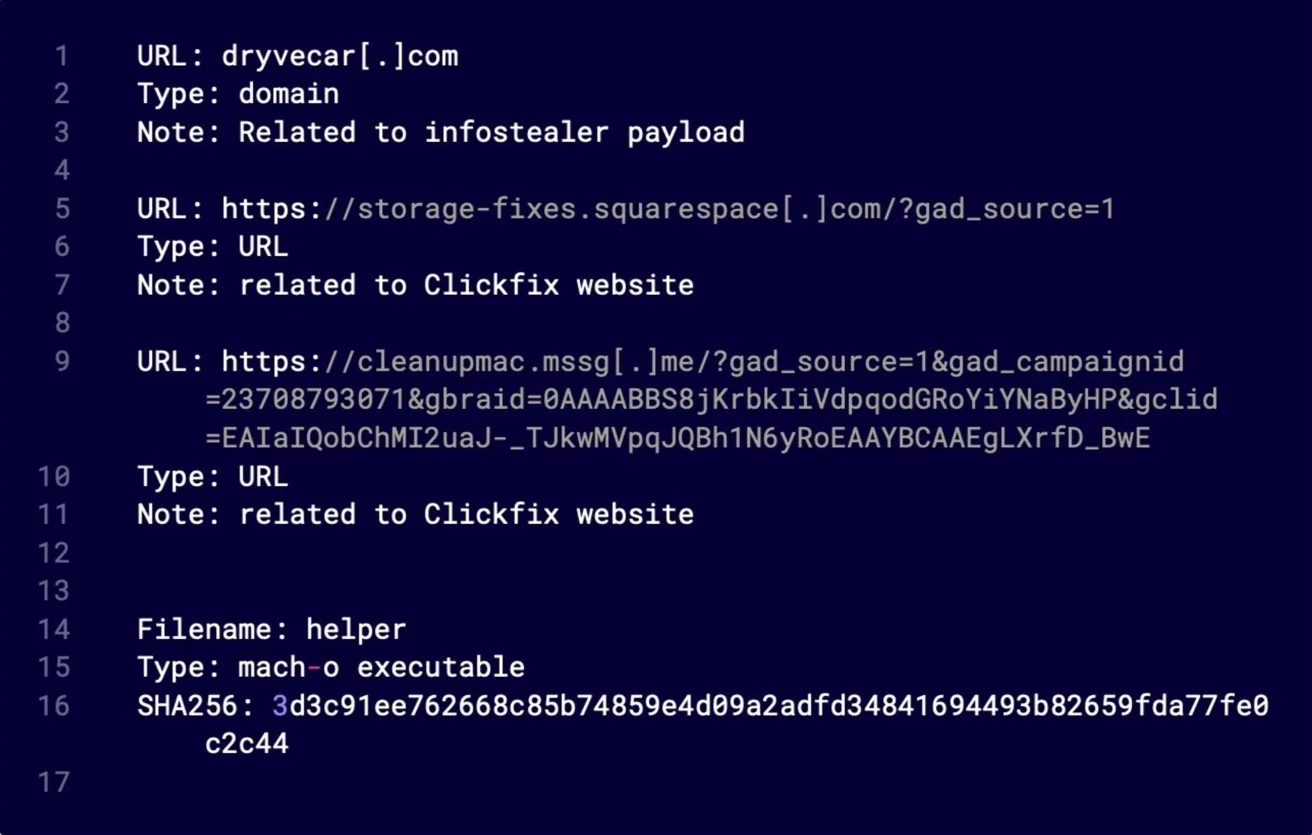
The attackers also adjusted their distribution strategy, creating a malicious webpage disguised as an official Apple website, falsely claiming that the user’s Mac had insufficient storage space. The page tricked the user into clicking the “Execute” button, triggering the applescript://URL protocol and directly launching the script editor application.
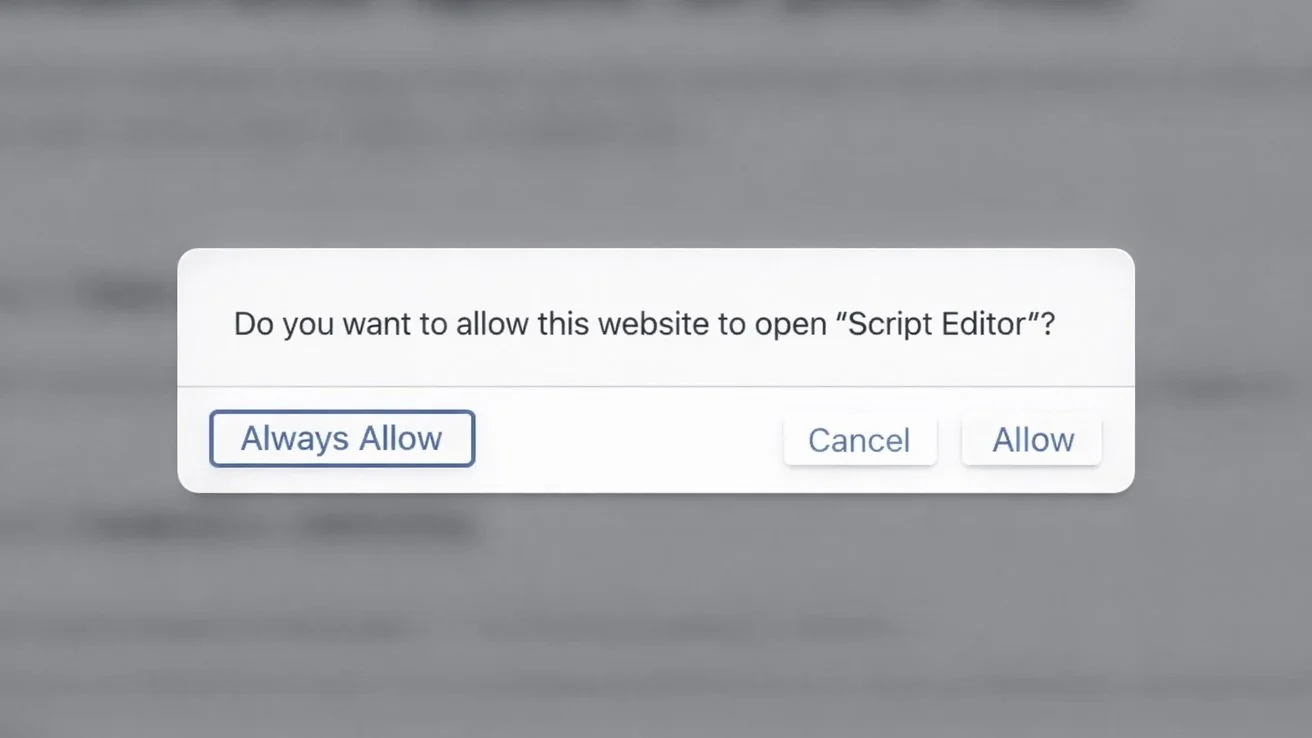
The browser then pops up a seemingly normal permission request. Once the user clicks “allow,” the script editor loads pre-installed malicious code. This browser-triggered-system-application pattern exploits the user’s trust in system tools, significantly increasing the success rate of attacks.
The malicious script runs obfuscated shell commands in the background, uses the tr tool to decode the hidden URL, downloads the remote payload via curl, and pipes it directly to zsh for execution in memory.
The second phase of the attack involves downloading the Mach-O binary to the /tmp directory, removing its extended attributes, marking it as executable, and then launching it. The Jamf security team confirmed that this payload is a variant of Atomic Stealer, specifically designed to steal sensitive system data.
This attack exposed a blind spot in macOS security. Apple had previously focused on strengthening the paste execution process in Terminal, but it did not fully cover the script editor execution path.
The attackers exploited this logical vulnerability, transforming the tedious process of manually entering commands into a seamless one-click experience triggered by the browser, making it harder for users to detect anything amiss.